What is Token Cracking?
Fortify security tokens that facilitate the flow of data between the user and the system to verify users and allow or refuse access.

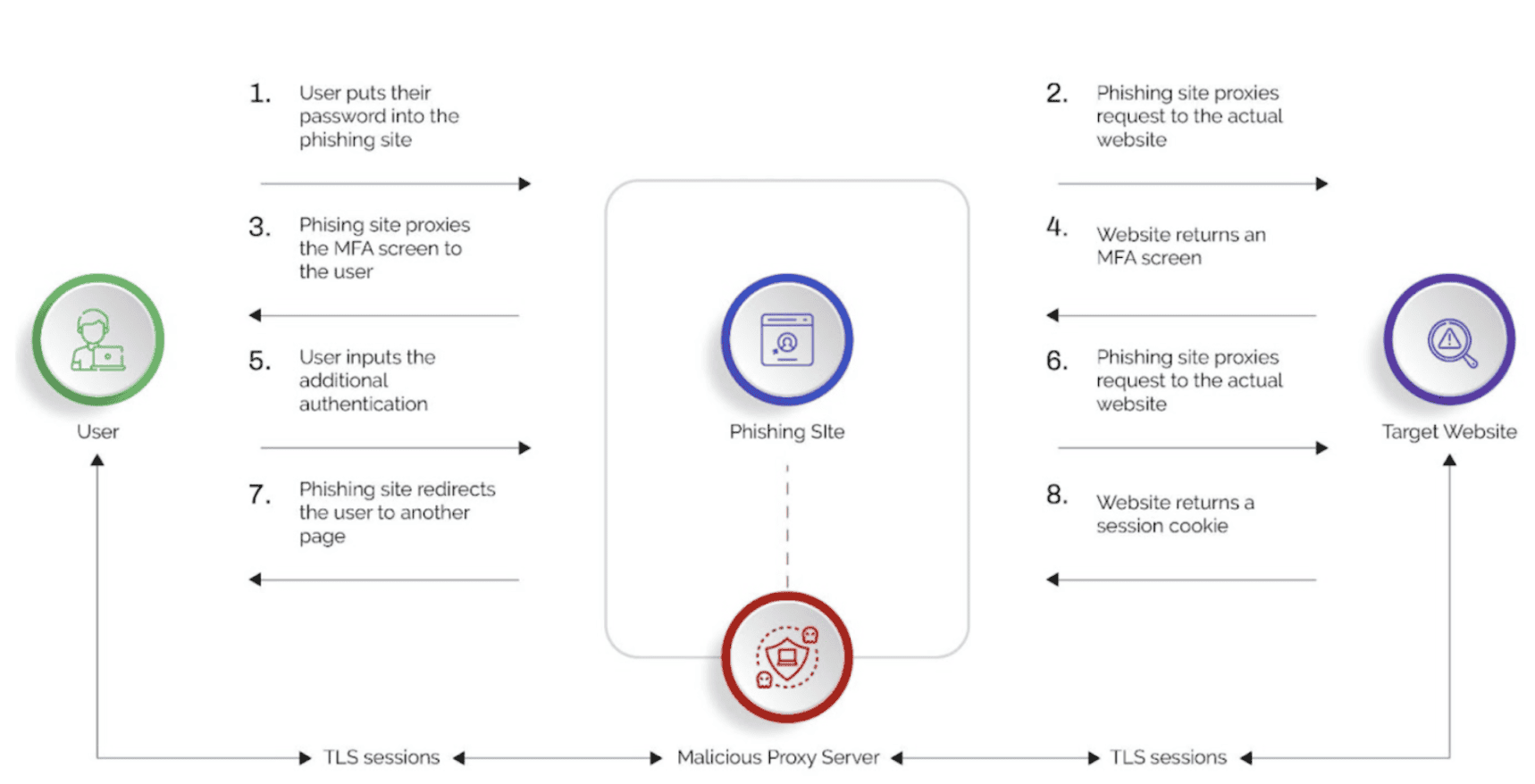
API HACKING” PART-6, OWASP TOP 10, JWT ATTACKS, by Madhumathi chamarthi
What Is OWASP Automated Threat (OAT – 019) – Account Creation
Trivia Crack The Board Game Based on Trivia App Game with Question Cards, Wager Tokens & Powerup Cards
Safe Cracker (pinball) - Wikipedia

What Is Broken Object Level Authorization? How To Prevent Such

Token - Crack Kills! - United States – Numista

Utility Tokens vs. Security Tokens: What's the Difference?
What is Token Cracking?
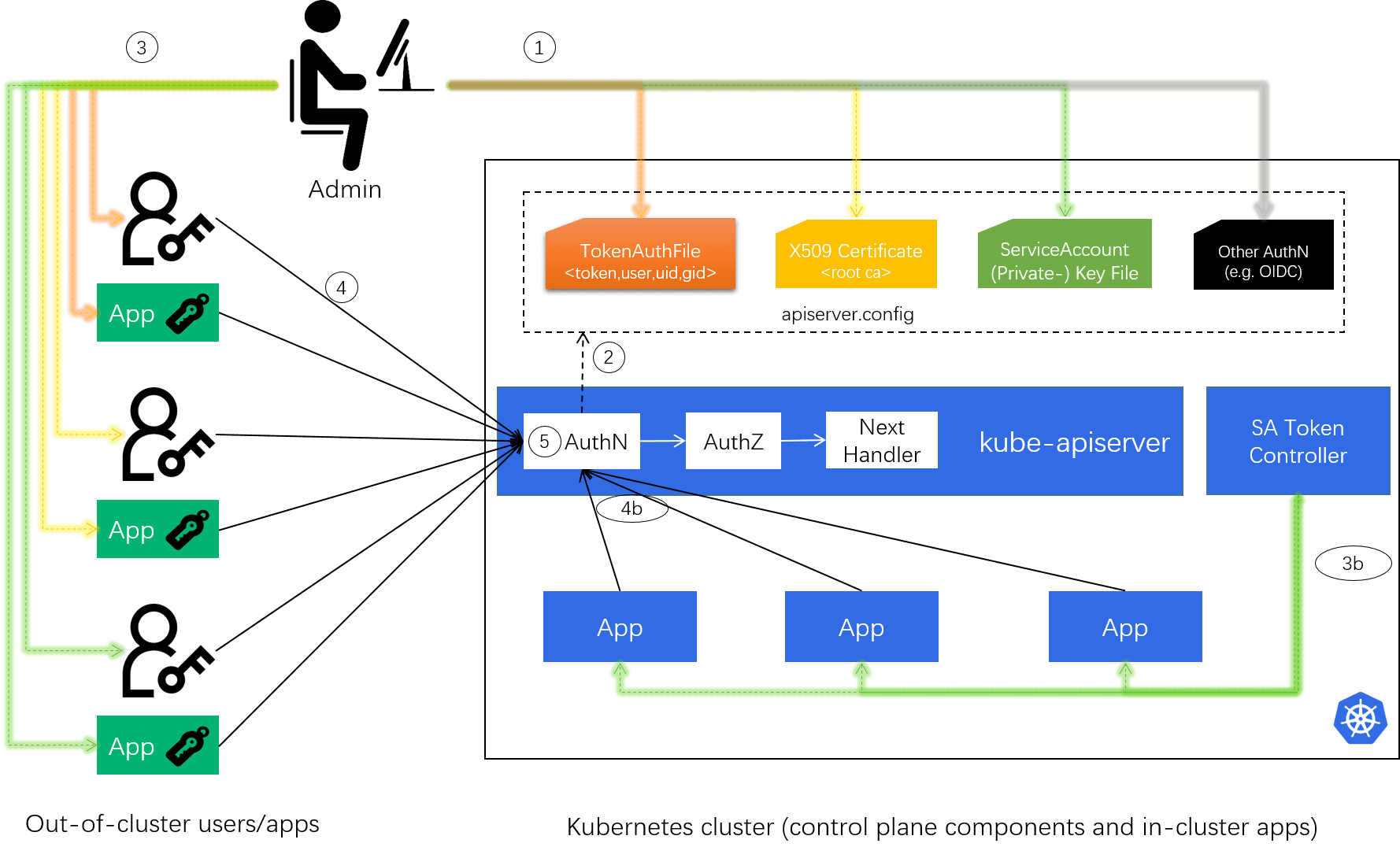
Cracking Kubernetes Authentication (AuthN) Model (2022)

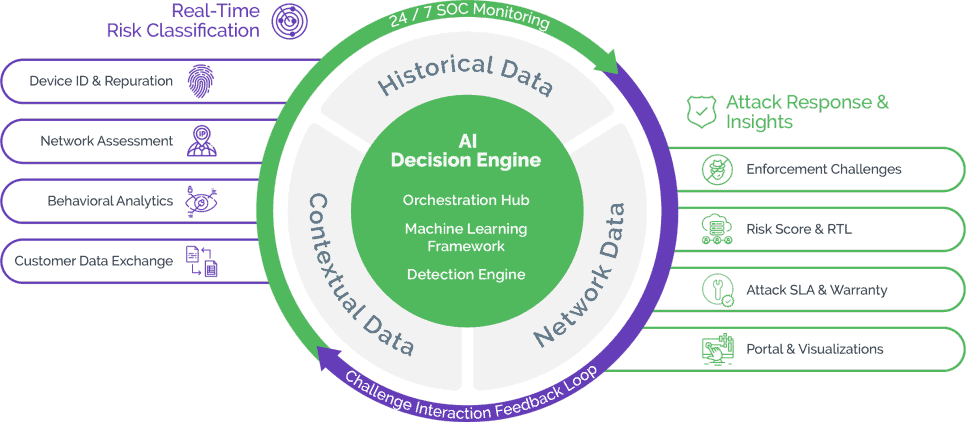
What Is Vulnerability Scanning? - Cloud WAF

Building a JWT Token Cracker with ZeroMQ & Node.js (Part 2.) - RisingStack Engineering

Tokens - Cardboard Crack

An illustration for crack probability-map generation and crack seed
What Is Vulnerability Scanning? - Cloud WAF

Animated Token, Did you know that there are animated Cardboard Crack tokens? They are really as cool as they sound. Check out the full collection here, By Cardboard Crack


:max_bytes(150000):strip_icc()/NFT_final-aa004ce971d24aecaa3f93688a35dec3.png)






